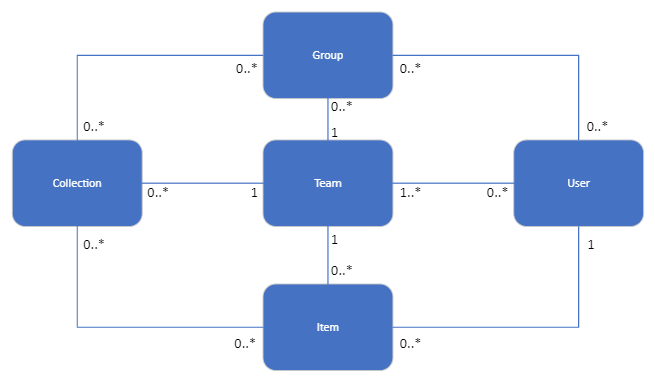
Bravura Safe entity relationships
Videos are available to help you to better understand the relationship of various entities used in Bravura Safe.
This video explains teams/collections/items/groups/users at a high level:
This video explains the management of teams/collections/items at a detailed level:
It describes the relationship between teams, collections and items and addresses the logic of when to create a new team or collection.
Bravura Security has a full YouTube playlist for Bravura Safe:
Teams: A central entity representing a group of users who share safe items. Enterprise teams are special; only one exists per tenant.
User: Represents an individual user within Bravura Safe.
Item: Represents a single safe entry.
Collection: A grouping of items within a team for access control purposes.
Group: Represents a group of users within a team with shared access permissions.
Team ↔ User (Many to Many): Users may be a part of multiple teams; however, may only be part of a singular enterprise team.
Team ↔ Collection (One to Many): A team can have multiple collections, but a collection belongs to a single team.
Collection ↔ Item (Optional) (Many-to-Many): A collection can have multiple items, and an item can belong to multiple collections.
Team ↔ Item (Optional) (One to Many): A team can have multiple items, but an item belongs to a single team (or user).
User ↔ Item (Optional) (One to Many): A user can have multiple items, but an item belongs to a single user (or team). The ability for a user to have items can be disabled by policy.
Group ↔ User (Many-to-Many): A group can have multiple users, and a user can belong to multiple groups.
Collection ↔ Group (Many-to-Many): A collection can be shared with multiple groups, and a group can have access to multiple collections.
Teams ↔ Group (One to Many): A group is a construct of a team, and only resides in the context of a team; therefore, a group can only belong to one team, and a team may have many groups.
Teams are a great way to create boundaries amongst the organization as a whole and are typically well suited to the following:
Departments
Divisions
Teams
Projects (useful for cross-department projects/initiatives)
Other special or sensitive applications (e.g. Office of the CEO, Investor Relations, etc.)
How broadly or fine-grained you define your Teams in Bravura Safe will often depend on how delegated or centralized you want management and administration of the tool to be. The more centralized, the fewer teams we recommend; the less centralized, the more teams we recommend.
The other aspect of centralization and decentralization worth mentioning is that a centralized schema in Bravura Safe puts more risk on Team or Enterprise Team owners. Whoever owns a team either already has – or can administratively – modify their access to get access to any items stored within the team. So, there is a risk introduced by breadth of access as well as the fact that these are "juicier" targets for compromise. On the other hand, it makes for easier provisioning and access management of Team members, since you can centrally administer invites, collections, groups, ACLs and cross-functional sharing.
Decentralization reduces the risk of consolidated access of team owners. It also means that provisioning and access management is put more into the hands of several different team owners representing different areas of the organization, which will likely produce more organic or fluid processes for provisioning and access management within each team.
There are pros and cons to both approaches.
Collections are a great way to organize credentials and secrets and control access to them within a team. They are often used to define what 'type' of credential resides within them. However, because items have a many-to-many relationship with collections, you can also use collections as a permission boundary to define 'sub-teams'.
Bravura Security (Enterprise Team)
Collections
Departmental Collections exist here
Top Level Company-Wide collection exists here
Policies:
Enterprise Wide SSO Policy and Reset Policy
Bravura Security Operations (Team)
Collections
Windows Local Admin Passwords
Windows Service Account Passwords
Unix Root Passwords
Groups
Windows Admin Team
Security Team
Unix Admin Team
ACLs:
Windows Local Admin Passwords
Groups:
Windows Admin Team: View/Edit
Security Team: View
Windows Service Account Passwords
Groups:
Windows Admin Team: View/Edit
Security Team: View
Unix Root Passwords
Groups:
Unix Admin Team: View/Edit
Security Team: View
Handling exception use cases is relatively easy. The easiest approach is to use Bravura Safe Share, as there is no need to add someone to a team just to share a single, one-off credential – it can easily be shared via Share. The recipient of the Share can then use the provided credentials directly. If they need to reference them again later, they can save these credentials into an Item within a team or collection of which they are a member, or simply save them within their own 'personal' safe.
Alternatively, as users can be part of multiple teams – for example, if someone on the Operations team above needed access to credentials owned by the Marketing team – they could be invited to the team and given access to only the relevant collection they need to view (and a collection could be made specifically for that purpose).